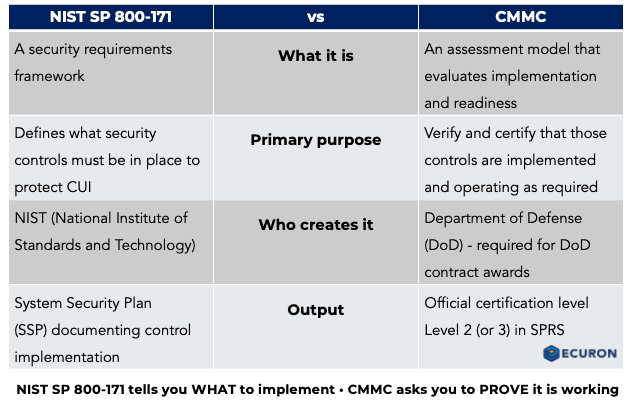
If your company handles Controlled Unclassified Information (CUI), you have probably seen CMMC and NIST SP 800-171 mentioned in the same conversation. That is one reason so many contractors assume they mean the same thing. They do not.
The short version is simple:
NIST SP 800-171 tells you what security requirements to implement.
CMMC is the DoD program that evaluates whether you have implemented those requirements well enough to achieve the required assessment result for contract award. For Level 2, that means an assessment against NIST SP 800-171 Rev. 2 using the CMMC assessment process and criteria.
That distinction matters. Many companies lose time and money because they focus on documentation without validating implementation, or they assume partial alignment with NIST SP 800-171 automatically means they are ready for a CMMC Level 2 assessment. The official assessment materials make clear that CMMC assessments look at evidence through examine, interview, and test, and results are captured at the assessment objective level, not just at the level of policy statements. If you are not sure what this means keep reading.
What Is NIST SP 800-171?
NIST SP 800-171 is a cybersecurity standard designed to help organizations protect Controlled Unclassified Information in nonfederal systems and organizations. In practical terms, it is the security baseline contractors are expected to implement when they handle CUI in their environments.
For CMMC Level 2 environments involving CUI, the relevant baseline is still NIST SP 800-171 Revision 2, not Revision 3. That point is important because many contractors see the “withdrawn” notice on Revision 2 and assume Revision 3 is now the CMMC expectation. NIST did withdraw Revision 2 and publish Revision 3, but DoD’s current CMMC guidance states that assessments are still being conducted against Revision 2 until the class deviation is withdrawn or superseded.
So while the market may already be talking about Revision 3, contractors preparing for CMMC Level 2 today still need to be grounded in Revision 2. That is where a lot of avoidable confusion starts.
What Is CMMC?
CMMC, or the Cybersecurity Maturity Model Certification, is the DoD program used to verify that contractors and subcontractors have implemented the required cybersecurity safeguards for the information involved in the contract. For Level 2, that means assessing implementation of the 110 requirements in NIST SP 800-171 Rev. 2. Depending on the solicitation, currently Level 2 may require either a self-assessment or a Certified 3rd Party Assessor Organization (C3PAO) assessment, and both paths also require annual affirmations.
In other words, CMMC is not just about whether a policy exists. It is about whether the control is actually working in the environment, whether the organization can demonstrate that clearly, and whether the scope is properly defined. The Level 2 assessment guide is explicit that evidence must be in final form and that a single NOT MET assessment objective can cause failure of the entire requirement.
The Biggest Difference
The easiest way to explain the difference is this:
- NIST SP 800-171 tells you what to implement.
- NIST SP 800-171A tells assessors how to evaluate whether it is really implemented.
- CMMC tells you what assessment path and status the DoD requires for the contract.
That is why companies that treat compliance as a paper exercise often run into trouble. A written policy may be necessary, but it is not enough on its own. Assessors will want to see that controls are operating in practice and that the organization can produce clear, supportable evidence.
Another point many defense contractors miss is that CMMC assessments are not really judged at the “we have 110 requirements on paper” level. They are judged at the level of the assessment objectives tied to those requirements. That is one reason organizations often overestimate readiness when they focus only on requirement statements and not on how those requirements will actually be assessed.
Why Contractors Get Confused
There are a few common reasons for the confusion:
- The terms are often used together in the same sales and compliance discussions
- Many organizations begin with NIST SP 800-171 and later realize they need to prepare for a more formal assessment path
- Internal teams may focus heavily on documentation and underestimate the importance of evidence and operational consistency
- Some teams mix current CMMC Level 2 expectations with newer NIST revisions, even though current CMMC Level 2 assessments are still tied to NIST SP 800-171 Revision 2
This confusion can create real delays. A company may spend months updating policies while leaving major scoping, access control, or evidence gaps unresolved. That is often where the real readiness problems are.
What This Means for Defense Contractors
If you are a defense contractor, subcontractor, or supplier handling CUI, the practical question is not just whether you understand the terminology. The real question is whether your environment, documentation, and evidence would stand up to review. For Level 2, that means being able to demonstrate that the NIST SP 800-171 Rev. 2 requirements are implemented and supported by evidence across the defined assessment scope.
That includes questions like:
- Where does CUI live in your environment?
- Which systems, assets, and users are in scope?
- Are your controls implemented consistently?
- Can you show evidence that those controls are functioning?
- Have you evaluated readiness at the level of the assessment objectives, not just the requirement titles?
- Have you identified weak points before a formal assessment?
These are the issues that often separate organizations that are making steady progress from those that keep reworking the same problems.
Common Mistakes to Avoid
Treating compliance as a documentation project
Policies matter, but they are only one part of readiness. If implementation is inconsistent, documentation alone will not solve the problem. CMMC assessments rely on examining documentation, interviewing personnel, and testing how controls operate in practice.
Defining scope too late
If you do not know what is in scope, remediation becomes inefficient and expensive. CMMC assessment scope is a formal concept, and scoping mistakes can distort everything that comes after.
Waiting too long to collect evidence
Evidence is often harder to assemble than teams expect. It should be gathered as controls are implemented, not only at the end. The assessment guide also makes clear that evidence must be final, not draft.
Assuming partial alignment means assessment readiness
A company may be on the right path and still not be ready for evaluation. Readiness requires clarity, consistency, and proof.
Overlooking the role of NIST SP 800-171A
Many contractors focus on the 110 requirements and do not assess themselves at the level of the related assessment objectives. That gap often leads to inflated self-assessment scores and a false sense of readiness. We often see scores drop by more than 100 points when a 3rd party assessment is performed. NIST SP 800-171A exists specifically to provide the assessment procedures and methodology used to assess the security requirements.
How to Prepare More Effectively
A more practical approach usually includes:
- Defining the CUI environment clearly
- Reviewing current controls against NIST SP 800-171 Revision 2
- Evaluating implementation at the level of the NIST SP 800-171A assessment objectives
- Identifying missing, weak, or inconsistent evidence
- Prioritizing remediation based on risk and effort
- Getting an independent view before moving too far ahead
This helps reduce wasted effort and gives leadership a more realistic picture of current readiness.
FAQ – CMMC vs. NIST SP 800-171
Is NIST SP 800-171 the same as CMMC?
No. NIST SP 800-171 is the security requirements baseline. CMMC is the DoD program used to assess whether those requirements have been implemented and whether the organization has the required status for award.
Does CMMC Level 2 use NIST SP 800-171 Revision 3?
No. Current CMMC Level 2 assessments are still conducted against NIST SP 800-171 Revision 2. DoD has said that remains the assessment basis until the class deviation is withdrawn or superseded.
What is NIST SP 800-171A?
NIST SP 800-171A provides the assessment procedures and methodology used to evaluate whether the security requirements in NIST SP 800-171 have been implemented effectively.
Why do companies struggle with this transition?
Because many teams focus first on policies and technical changes without fully addressing scope, evidence, ownership, repeatability, and the level of detail reflected in the assessment objectives.
What should we do first?
Start by identifying where CUI exists, what systems and assets are in scope, and where your biggest gaps are likely to be. And do not forget about Federal Contract Information (FCI). If a contract involves only FCI and not CUI, the relevant CMMC requirement may be Level 1 rather than Level 2.
Conclusion
Understanding the difference between CMMC and NIST SP 800-171 is not just a terminology issue. It affects how you plan, prioritize, and prepare.
For CMMC Level 2, NIST SP 800-171 Revision 2 gives you the security requirements and NIST SP 800-171A gives you the assessment detail many organizations overlook. CMMC does not change the underlying Level 2 control baseline, but it does add formal assessment, affirmation, and status requirements. At Level 3, CMMC also adds selected NIST SP 800-172 requirements.
For many contractors, the smartest next step is an independent gap assessment that shows where they stand now, what needs attention first, and how to move forward with less guesswork.
If you are unsure whether your current NIST SP 800-171 efforts will hold up under a CMMC assessment, Ecuron can help you identify gaps, clarify scope, and build a more practical path toward readiness.